Mathieu Tartare
@mathieutartare
Malware Researcher at @ESETresearch
@[email protected]
ID:51153948
https://www.welivesecurity.com/en/about-eset-research/ 26-06-2009 17:53:50
319 Tweets
531 Followers
520 Following

#ESETResearch is releasing Nimfilt, an #IDAPro plugin to help reverse engineering #Nim malware – a language increasingly used by both the red-teaming community, and malware developers. Nimfilt demystifies Nim's custom mangling scheme. github.com/eset/nimfilt Barberousse @[email protected]
1/3

Our latest report on a CN #APT targeting tens of governments entities worldwide has been published 🥳 After monitoring it for a long time we realized it is likely related to the recent I-Soon company leaks. It discusses their TTPs and provides lots of IOCs trendmicro.com/en_us/research…

#ESETresearch has discovered a new campaign by 🇨🇳China-aligned #APT #EvasivePanda , leveraging the Monlam Festival to target Tibetans. The campaign included a targeted watering hole, compromised news website, and an additional supply-chain attack ... welivesecurity.com/en/eset-resear… 1/7



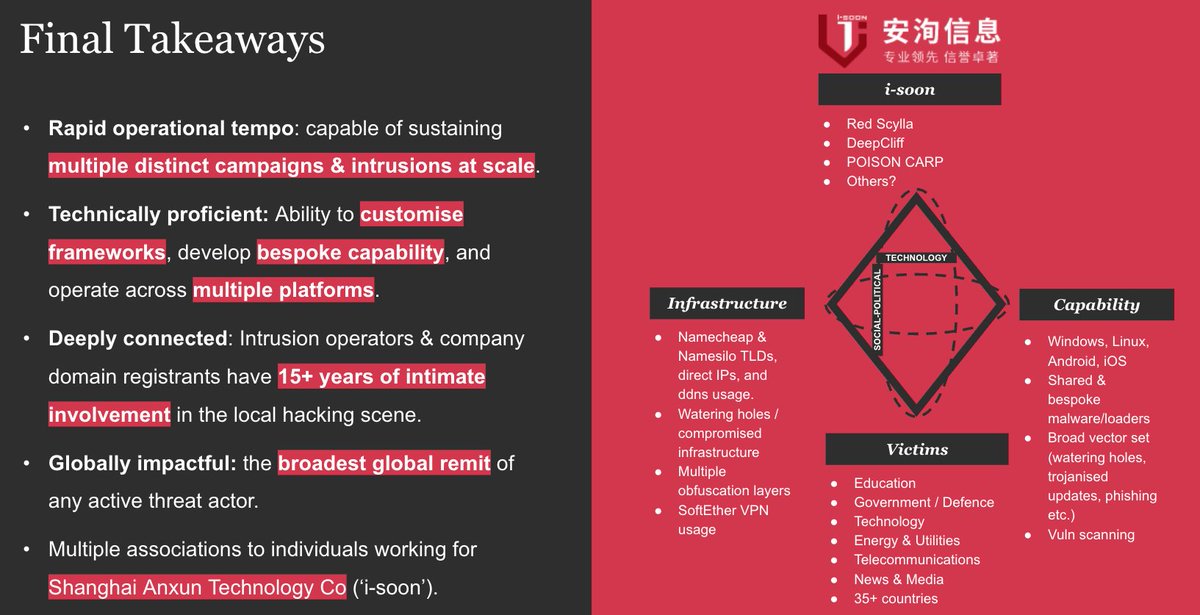
These relationships, technical indicators, and related public reporting from Trend Micro Research Recorded Future and others, drew many links to i-Soon, and painted a picture of them as one of the most pervasive, capable China-based actors in recent history.


#threatintel
someone just leaked a bunch of internal Chinese government documents on GitHub
github.com/I-S00N/I-S00N/

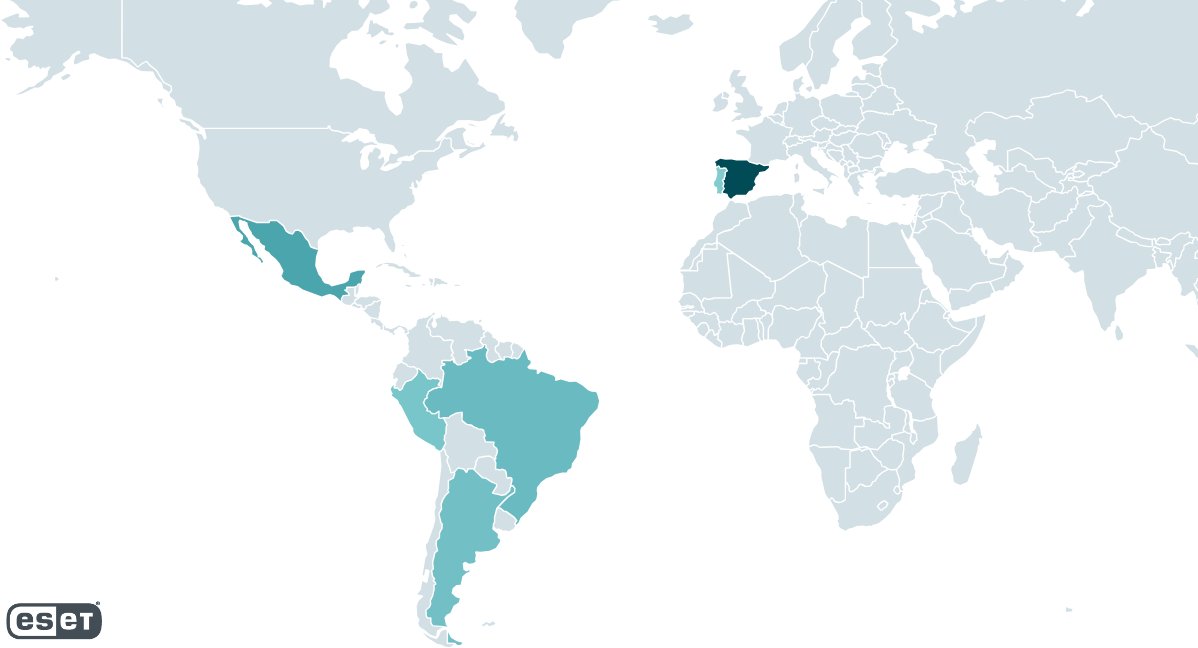
#ESETresearch aided in an operation to disrupt #Grandoreiro , a banking trojan targeting the general public in 🇧🇷, 🇲🇽, 🇪🇸 and 🇦🇷. ESET provided technical analysis, stats, and C&C addresses. welivesecurity.com/en/eset-resear… 1/4

#ESETresearch has discovered a China-aligned APT group, which we named #Blackwood , that leverages adversary-in-the-middle (AitM) to deliver the NSPX30 implant via software updates. NSPX30 is a sophisticated implant evolving since at least 2005. facundo Mz welivesecurity.com/en/eset-resear… 1/6

🚨 Unveiling #Blackwood : A China-aligned APT group delivering the NSPX30 implant via adversary-in-the-middle attacks since 2005. Learn how this sophisticated threat is delivered through software updates and its impact on targeted individuals and companies.
#ProgressProtected

ESET Threat Report H2 2023: the 2nd half of 2023 saw various incidents, such as Cl0p’s MOVEit hack, the abuse of the word ChatGPT in malicious domains, and the demise of the Mozi botnet. Learn about the threat landscape in the report, out now web-assets.esetstatic.com/wls/en/papers/… #ESETresearch



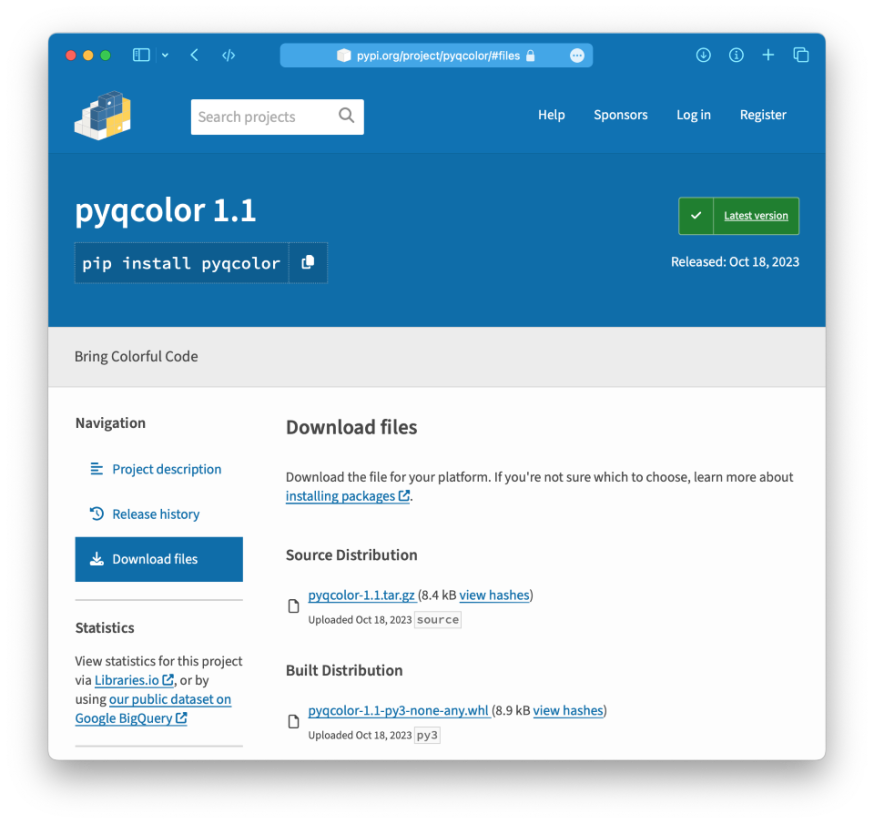
#ESETresearch warns about malicious Python packages in the official @PyPI repository that target Windows and Linux. This cluster shares metadata or has similar payloads, and seems different from the one we reported in May: x.com/esetresearch/s…. Marc-Etienne M.Léveillé 1/6


'quand Internet est cassé, c'est souvent chez les mêmes [...] Celles et ceux qui tentent de résister à l'effacement, celles et ceux dont la voix nous parvient, faiblarde et distordue, entre deux glitchs, comme à travers une radio pirate.' - Merci Thibault Prévost pour cette chronique

#ESETResearch discovered a zero-day XSS vulnerability ( #CVE -2023-5631) in Roundcube Webmail servers. It is actively used in the wild by #WinterVivern to target governments and a think tank in Europe. The exploit was contained in a legitimate-looking email about Outlook. 1/4