Don’t miss our special guest, ATT&CK's Jamie 🔜 RSAsí 🌉, in our in-booth theater session on May 8 at 1:30pm at #RSAC booth #1543 in the South Hall, covering “What's Happening with MITRE ATT&CK for Mobile.” #MobileAppSecurity #MobileDeviceSecurity #MobileSecurity


Headed to RSA Conference next week? Jamie 🔜 RSAsí 🌉, Adam Pennington, and Joe Słowik 🌻 from the ATT&CK team are too! Interested in meeting up? @mitreattack's DMs are open, or stop by the MITRE booth at 3430.


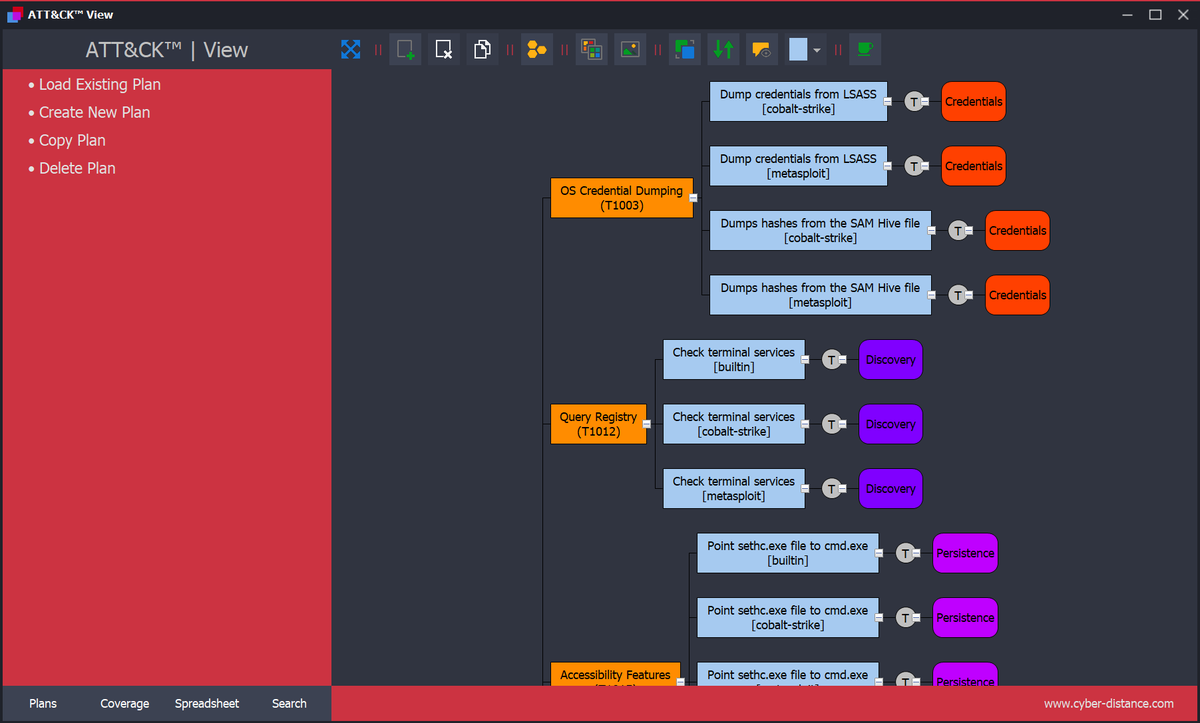
ATT&CK View and the Relational Data model are updated to reflect on ATT&CK V15.0 & latest Red Canary ATOMIC tests
Blog: wix.to/dIQIcX6
The import tools source code and import process will follow.
Thanks to Embarcadero Tech for supporting me with your dev tools.

Validato can help you understand how effective your security controls are at detecting and protecting your business from critical MITRE ATT&CK Techniques.
#cybersecurity #validato #cybermeme #mitreattack


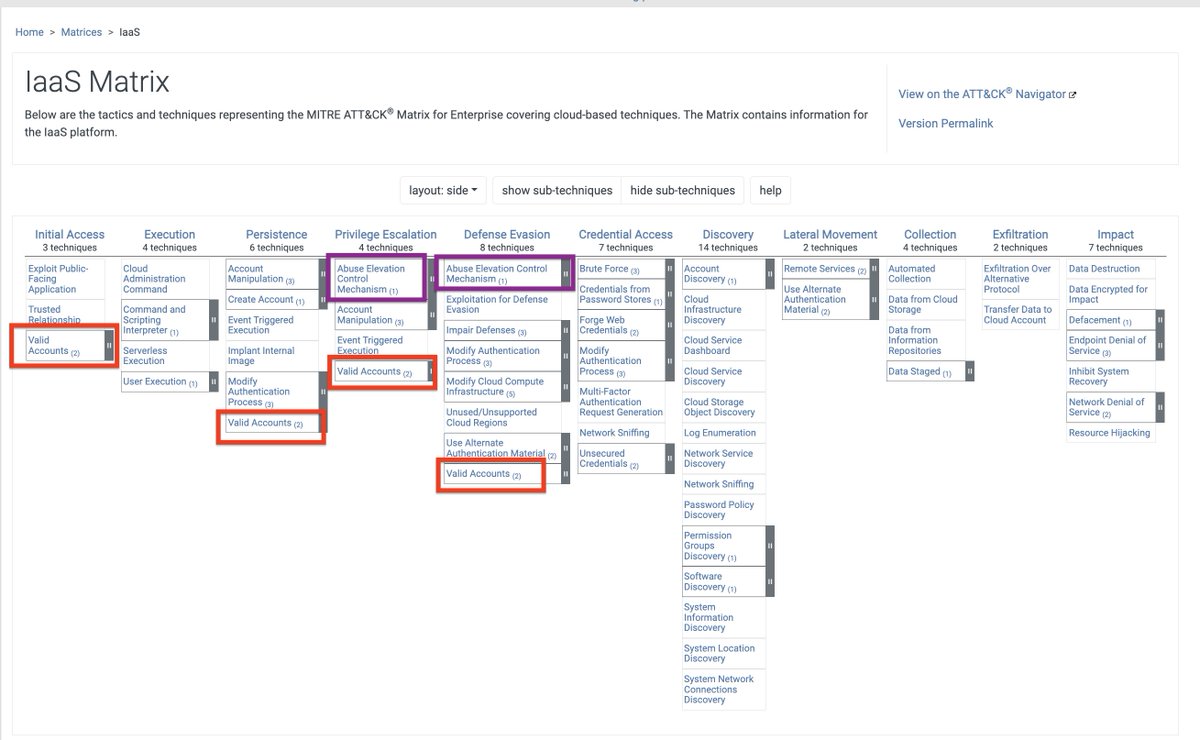
Chester Le Bron ATT&CK Chester Le Bron , some ATT&CK techniques are repeated across several Tactics, so it is not really an issue with the AWS Cloudtail event names. In the image below, you see the 'Valid Accounts' appear under 4 different Tactics ...similar repetition with 'Abuse Elevation Control…

Honored to present at the Asia-Pacific ATT&CK Community Workshop 2024 in Singapore! Our speakers, Till Jäger and Vini Engel, shared insights about The Magic Cross-Platform Threat Detection.
#MITRE #threatdetection #cybersecurity #threathunting #BlueTeam ATT&CK



📈 Boost your #SecOp team's #Cybersecurity readiness!
Our Threat-Informed Defense 101 Guide details how to evaluate your #Security using the MITRE ATT&CK framework, enhancing visibility into control effectiveness.
Claim your copy below! 👇
bit.ly/45MxFSD #MITREATTACK



🤯 #Ransomware attacks are up 95%!
In a @Betanews Q&A, AttackIQ's Andrew Costis highlights why proactive #Cybersecurity measures and the #MITREATTACK framework are more important than ever.
Read about our approach to combating these advanced threats. 👉 bit.ly/3JBx5yq



🚨The mentioned zero-day flaws can be weaponized by threat actors to bypass authentication and run arbitrary commands on the infected system.
Read more here:
thehackernews.com/2024/04/mitre-…
#cybernews
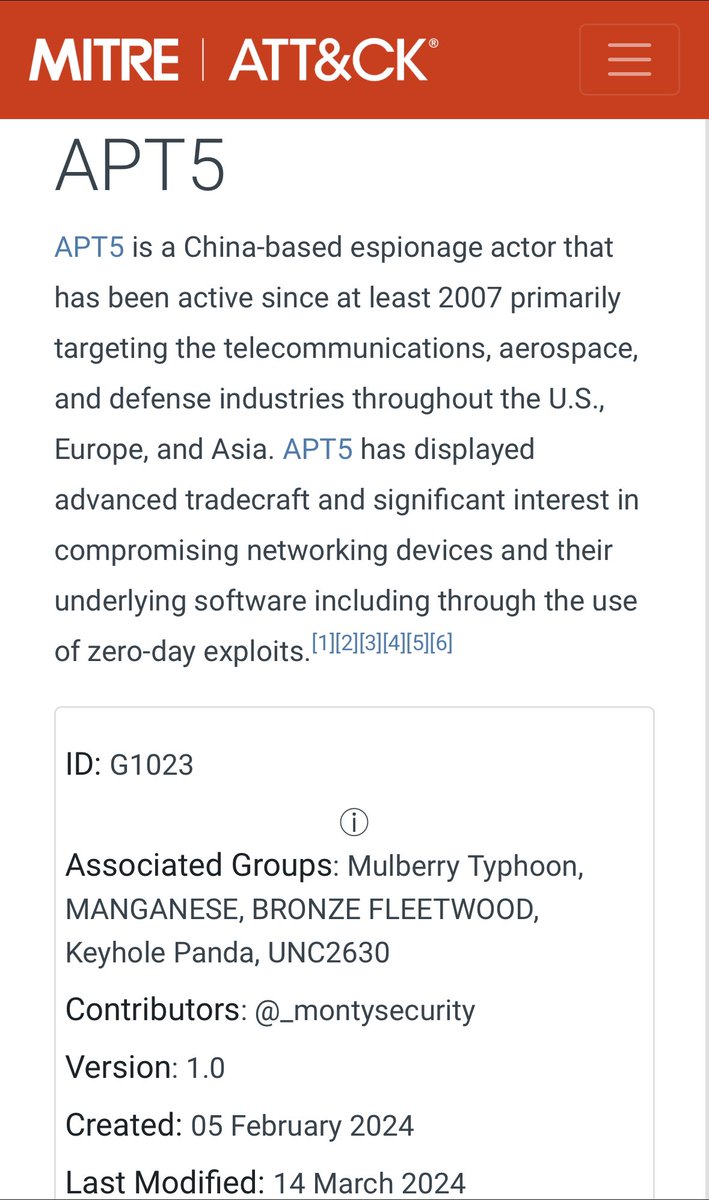
#cybernews monday #mitreattack #cybercrime #malware #threatactor