
Zuzana Hromcova
@zuzana_hromcova
Malware Researcher @ESET
ID:986711115769016320
https://www.welivesecurity.com/en/ 18-04-2018 21:00:37
33 Tweets
1,0K Followers
71 Following


#BREAKING #ESETresearch helped analyze a #Sandworm campaign against an energy company in #Ukraine 🇺🇦 using #CaddyWiper and a new version of the infamous #Industroyer malware. #WarInUkraine welivesecurity.com/2022/04/12/ind… 1/5

Breaking. #ESETResearch discovered a new data wiper malware used in Ukraine today. ESET telemetry shows that it was installed on hundreds of machines in the country. This follows the DDoS attacks against several Ukrainian websites earlier today 1/n

New #ESETresearch blogpost discusses vulnerabilities among kernel drivers, provides several case studies of malware utilizing such drivers, shows examples of discovered CVEs, and outlines mitigation techniques. welivesecurity.com/2022/01/11/sig… 1/5

Tired of reading? From now on, you can switch to the audio and listen to ESET Research via our new ESET Research podcast. Find it on Spotify, Apple Podcasts, Google Podcasts as well as on PodBean. esetresearch.podbean.com 1/3




NEW RESEARCH 📢📢: Amnesty Tech has published a investigation revealing a hacker-for-hire style campaign targeting a prominent activist from Togo in West Africa. Lets dive into this curious case.. THREAD
amnesty.org/en/latest/news…

#ESETresearch has discovered a new undocumented UEFI bootkit, #ESPecter , persisting as a patched Windows Boot Manager (bootmgfw.efi) on the Efi System Partition (ESP). welivesecurity.com/2021/10/05/uef… 1/5 Martin Smolar Anton Cherepanov


Don’t miss #ESETResearch presentation “The #Winnti Group: an analysis of their latest activities” at #Botconf2020 . See you virtually on Thursday at 13:50 (UTC+1, Paris Time). Mathieu Tartare
botconf.eu/botconf-2020/s…

Recently discovered by #ESETresearch Martin Smolar, #ModPipe modular #backdoor is hungry for data, targeting sensitive information stored in management software suite used by hundreds of thousands of bars, restaurants and hotels worldwide. welivesecurity.com/2020/11/12/hun… 1/4


[1/n] I'm happy to share a significant research done by Igor Kuznetsov and myself. What we found was a UEFI rootkit in the wild, customized from Hacking Team's leaked Vector-EDK code. That would be the second time we see something like this publicly
securelist.com/mosaicregresso…


#ESETResearch analyzed various post-compromise tools used by the #Gamaredon group to steal sensitive documents and spread in their victim’s networks including custom MS Outlook VBA projects and macro injection tools welivesecurity.com/2020/06/11/gam… Jean-Ian Boutin 1/4


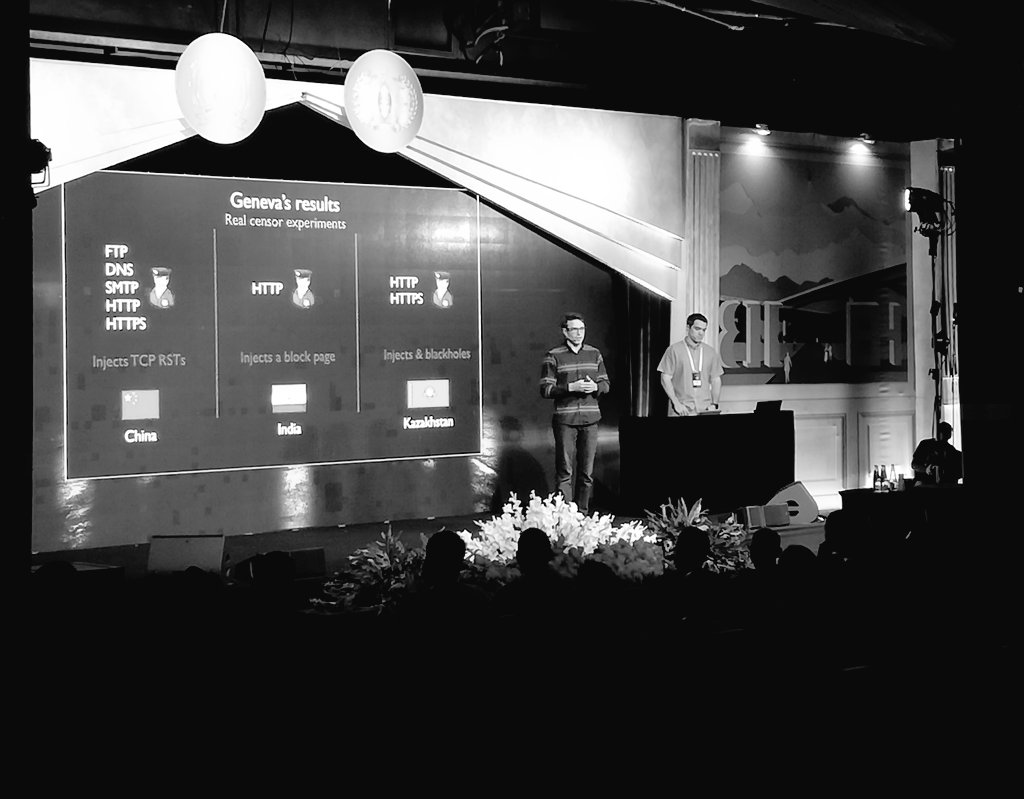
VERY interesting talk BlueHat IL on evading #censorship using #AI ! Also with impressive results from real-world tests. Well worth checking this research! geneva.cs.umd.edu

How can #Richheaders be leveraged for malware hunting? Peter Kálnai & Michal Poslusny from #ESETresearch discussed this mysterious artifact at the #AVAR2019 #cybersecurity conference avar2019.org/agenda/day-1/r…


Starting with the telemetry data gathered by ESET’s #UEFI scanner, #ESETresearch machine learning specialists and malware researchers devised a method to spot rare UEFI/based #malware . #cybersecurity
welivesecurity.com/2019/10/08/nee…